Are you interested in delivering a webinar presentation on your DoD research and engineering efforts?
CSIAC hosts live online technical presentations featuring a DoD research and engineering topic within our technical focus areas.
Host a Webinar with CSIAC
Upcoming Webinars
Deceptive AI: Understanding and Defending Against the Next Generation of Cyber Weapons
COMING SOON – EXACT DATE AND TIME TBD. In the evolving theater of modern warfare, artificial intelligence (AI) has emerged as a transformative force and new frontier of vulnerabilities. This presentation provides a critical analysis of…
Past Webinars
Open-Source Security and Generative AI: Navigating Concerns While Enhancing Development
This webinar will explore the impact of OpenAI’s ChatGPT, GitHub CoPilot, and other generative artificial intelligence (AI) tools on open-source software and security. With over…
Uncomfortable Truths About Cybersecurity
In this webinar, participants will drill into the history of cybersecurity and computer science and consider some first principles. Decisions made in the 1970s by…
Fundamentals of Cross-Domain Solutions in the DoD
A cross-domain solution (CDS) is a capability that can be used to securely connect discrete systems or networks, which may have different security policies to…
Developing the Cybersecurity Workforce: An Introduction to the NICE Framework
The Workforce Framework for Cybersecurity (National Initiative for Cybersecurity Education [NICE] Framework) (NIST SP 800-181r1) establishes a common language for describing cybersecurity work and what…
Optimization Techniques: Improving Effectiveness for Defense Simulation Models
When performing defense system analysis with simulation models, a great deal of time and effort are expended, creating representations of real-world scenarios in U.S. Department…
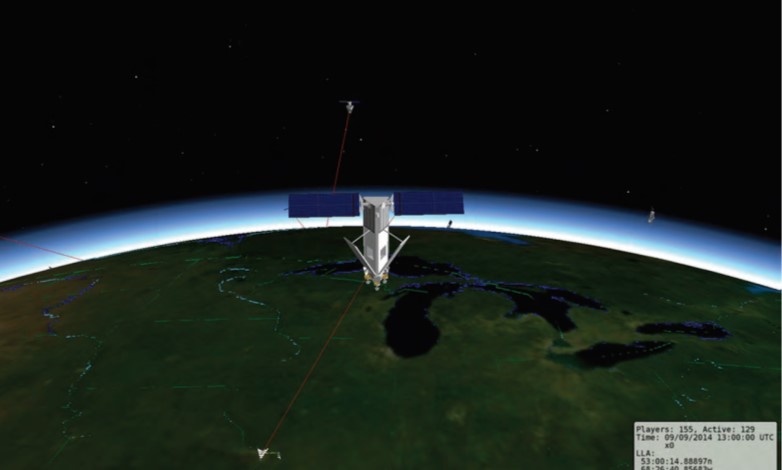
Modeling and Simulation on the Final Frontier With AFSIM
The Advanced Framework for Simulation, Integration, and Modeling (AFSIM) is a government-owned, military simulation framework that enables users to perform complex mission-level simulations for analysis…