Are you interested in delivering a webinar presentation on your DoD research and engineering efforts?
CSIAC hosts live online technical presentations featuring a DoD research and engineering topic within our technical focus areas.
Host a Webinar with CSIAC
Upcoming Webinars
Deceptive AI: Understanding and Defending Against the Next Generation of Cyber Weapons
COMING SOON – EXACT DATE AND TIME TBD. In the evolving theater of modern warfare, artificial intelligence (AI) has emerged as a transformative force and new frontier of vulnerabilities. This presentation provides a critical analysis of…
Past Webinars
M&S Support for Cyber Mission Forces
Presentation by Dr. Steven King, Deputy Director, Cyber Technologies, OASD (R&E).
Discussion on Cyber M&S moderated by Michael Weir
Cyber M&S discussion moderated by Michael Weir, Director of Cybersecurity and Information Systems Information Analysis Center (CSIAC).
Breakout Group Summaries on Cyber M&S
Afternoon breakout groups present summaries and conclusions on Cyber M&S.
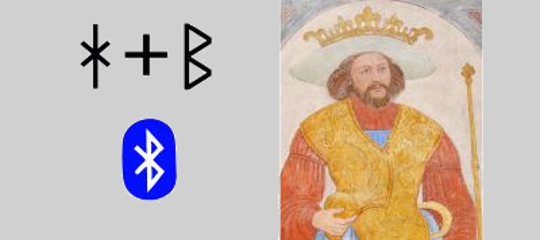
Bluetooth
Key facts and figures on Bluetooth, and some tips on how maintain a good security posture in a world of increasingly popular Bluetooth devices.
Asymmetric Resilient Cybersecurity
We are delivering the theory, processes, methodologies, and algorithms that will enable a resilient cyber infrastructure with an asymmetric advantage to thwart adversaries who seek…
Next Generation Service Model Architectures
Modern networked computing systems are becoming increasingly more complex. The recent explosion of the Internet of Things (IoT), ranging from mobile embedded devices to large…