Are you interested in delivering a webinar presentation on your DoD research and engineering efforts?
CSIAC hosts live online technical presentations featuring a DoD research and engineering topic within our technical focus areas.
Host a Webinar with CSIAC
Upcoming Webinars
Deceptive AI: Understanding and Defending Against the Next Generation of Cyber Weapons
COMING SOON – EXACT DATE AND TIME TBD. In the evolving theater of modern warfare, artificial intelligence (AI) has emerged as a transformative force and new frontier of vulnerabilities. This presentation provides a critical analysis of…
Past Webinars
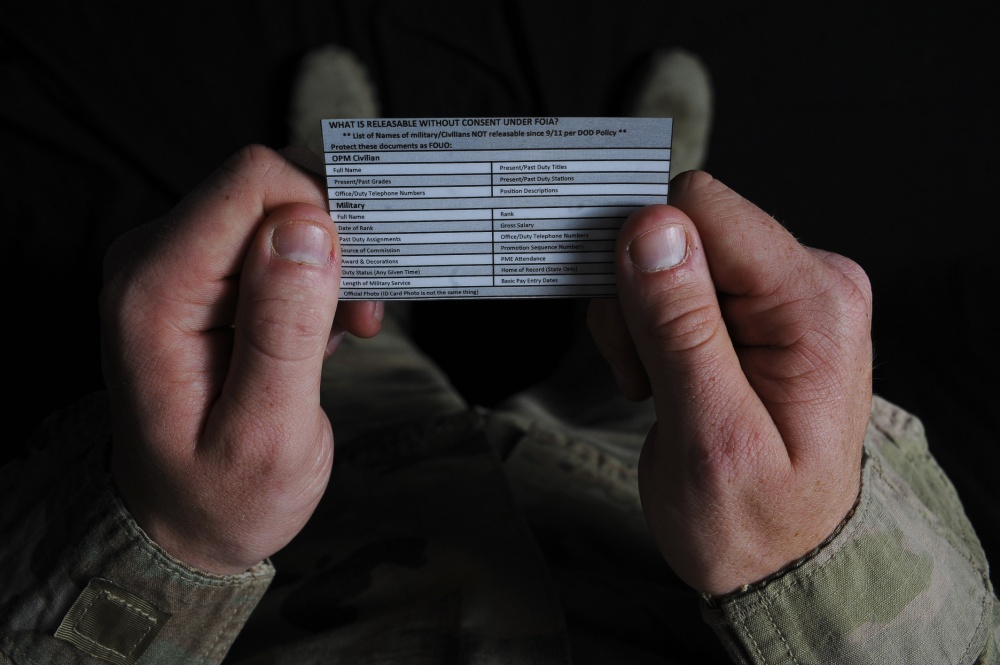
Personally Identifiable Information (PII) – What is it?
Learn about Personally Identifiable Information (PII).
Democratize Anomaly Detection Technologies: Challenges, Advances, and Opportunities
The mature signature-based intrusion detection technology has been the first line of defense in the cyberspace. However, due to the perpetual cat-and-mouse game and asymmetry…
Insider Threat: Possible Indicators
An insider threat is a malicious threat to an organization that comes from people within the organization. Learn how to spot some possible indicators of…
CryptoLocker: Surviving a Ransomware Attack
CryptoLocker is exploding and organizations large and small are being hit with ransomware attacks that hold their computers and networks hostage in exchange for ransom….
Password Tips
Learn some helpful tips to make a more secure password.
Comply to Connect (C2C)
The challenging era of the Joint Information Environment (JIE) and Internet of Things (IoT) will require increased situational awareness and better control over the traffic…