Are you interested in delivering a webinar presentation on your DoD research and engineering efforts?
CSIAC hosts live online technical presentations featuring a DoD research and engineering topic within our technical focus areas.
Host a Webinar with CSIAC
Upcoming Webinars
Deceptive AI: Understanding and Defending Against the Next Generation of Cyber Weapons
COMING SOON – EXACT DATE AND TIME TBD. In the evolving theater of modern warfare, artificial intelligence (AI) has emerged as a transformative force and new frontier of vulnerabilities. This presentation provides a critical analysis of…
Past Webinars
Agile, Energy-Efficient, and Trustworthy Intelligence at the Edge
Artificial intelligence (AI) has become the linchpin in a growing number of products, services, and research programs which are aimed at automating and enhancing the…
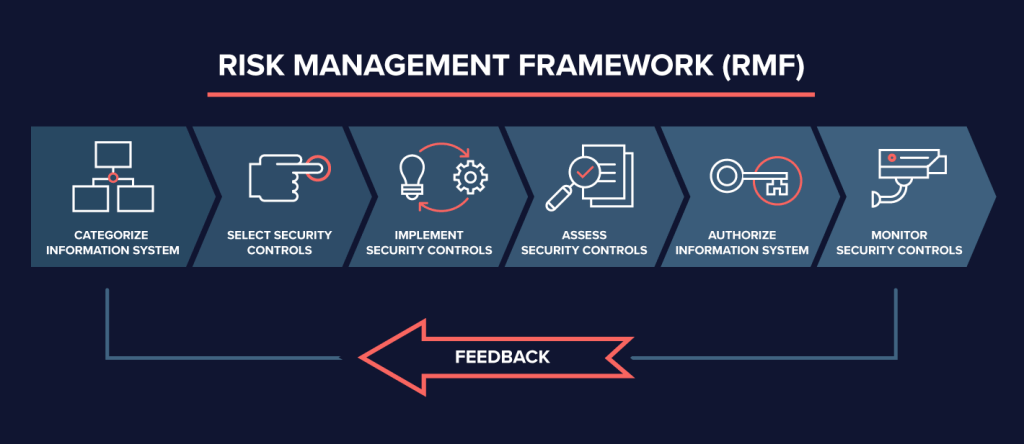
Risk Management Framework (RMF) Categorization Part 1-4
In this four part podcast series, CSIAC subject matter experts (SMEs) conduct a roundtable discussion of the first step of the Risk Management Framework (RMF)…
What Is Machine Learning Anyway?
Machine learning (ML) appears to be the ubiquitous go-to solution for a great many modern problems across many domains. But what is really under the…
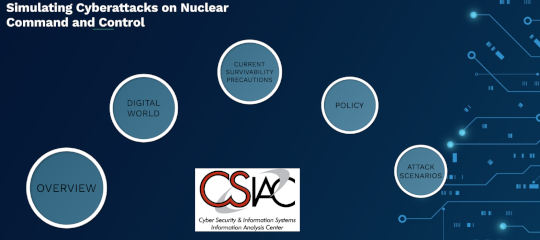
Simulating Cyberattacks on Nuclear Command and Control
During the height of the Cold War, the biggest fear involved the possibility of mutually assured destruction (MAD) from nuclear warfare. However, in today’s digital…
Cybersecurity Simplified
To many, cybersecurity is a well-known but poorly understood topic. System owners specializing in non-software/Information Technology (IT) functions have undoubtedly been warned of the potentially…
Highly Secured Blockchain Technology for Strategic Supply Chain Management
The blockchain technology is a game changer to enhance the security of our supply chain, and smart manufacturing. The technology enables the tracking and recording…